AS2 Listener
The AS2 Listener receives incoming messages from an AS2 server via HTTP Post request. It is able to handle all forms of encryption, signature validation, and compression that are defined in the AS2 protocol.
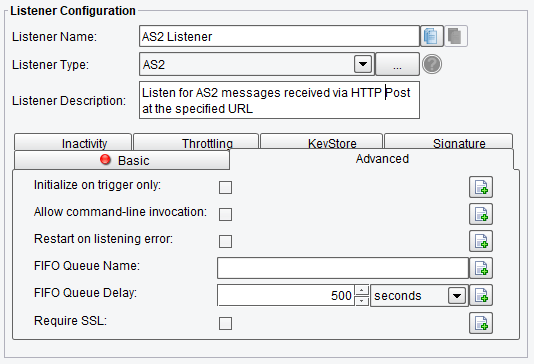
1. On the Basic tab, you can specify the request path of the HTTP endpoint to receive messages.

2. On the Advanced tab you can set the maximum number of transactions to process at a time; whether or not sub-folders should be searched for files as well; whether or not reads in all matching files as a single stream; a number of lines to treat as header lines (the header of the first file is included and skipped in all other files); a regex expression which must be contained by the full folder path of the file to be picked up (typically will only be used if you are using the ‘Include sub-folder’ option).
- Initialize on trigger only – If enabled, the Listener doesn’t start up until a trigger initializes it.
- Allow command-line invocation – If enabled, the listener can be invoked using the CLI client application.
- Restart on listening error – If enabled, the listener will be restarted after an error occurs.
- FIFO Queue Name – The FIFO field enables a “First In, First Out” queuing mechanism between Listeners and Transports. If a “FIFO Queue Name” is provided, that name will be used as a key for a queue Transactions & will be pushed into before reaching a transport. They’ll be ordered in this queue according to when the Listener created them.
- FIFO Queue Delay – It is the interval between updates/checks against that queue. Providing a queue name guarantees that a given Transport sends Transactions in the same order the Listener created them in.
- Require SSL – If selected, plain text requests will be rejected.
3. On the Inactivity you can specify:
- Enable Inactivity Monitor – Check this box to enable inactivity monitoring. This will throw a non-transaction exception if the specified number of transactions haven’t been processed in the specified time interval.
- Min. Transactions to Expect – The number of transactions to expect to be completed per monitoring interval.
- Monitoring Interval – How often to check the specified number of transactions have been processed.
- Times to Monitor – If set, monitoring will be done during the defined times of day. To ignore, set start and end time equally.
- Days to Exclude from Monitoring – Inactivity monitoring will not occur on the days specified.
- Include Errors in Transaction Count – If checked, transactions that attempted to start but failed at the Listener stage will also be counted.

4. On the Throttling you can specify:
- Throttling Mode – The throttling mode to use for limiting the number of transactions or messages emitted by this Listener. “Timed” will limit transactions based on time intervals, while “Concurrent” will limit based on a concurrent number of transactions. “Concurrent” mode requires a Throttling Response Processor step later in your Interface workflow to acknowledge completion.
- Throttling Mechanism – The mechanism to use for throttling message. “Blocking” prevents the Listener from continuing to process and emit messages altogether, while “Queued” pushes received messages into the Interface queue (or a default, in-memory queue).
- Max Concurrent Messages – How many messages can be concurrently processed, either by time-based limits (“Allow X per Second”) or synchronous (“Allow X at any Time”)
- Timed Emission Interval – The interval for time-based limits (“Allow X per X Timed Emission Interval”)
- Synchronous Timeout Interval – The interval to wait for a synchronous response before failing.

5. On the KeyStore tab, you can specify:
- KeyStore Path – The path to the KeyStore file where the decryption key is stored.
- KeyStore Type – The type of KeyStore. We support PKCS12, JKS, and JCEKS KeyStore types.
- KeyStore Password – If needed, password to unlock the KeyStore.
- Decryption Key Alias – The alias of the private key to be used for decryption.
- Decryption Key Password – If the private key is password-protected, this is where that password can be provided. If no password is needed, leave blank.

6. The Signature tab. If the AS2 sender signs their messages, the Signature tab is where the certificate file can be provided for signature verification.

