Asymmetric Decryption Processor
Asymmetric Decryption Processor decrypts input data using a supplied private key and verifies its signature. It is currently distributed only in the United States.
Encrypt and Decrypt Data with the eiConsole’s Encryption and Decryption Processors
The Encryption and Decryption Processors in the eiPlatform Integration Engine and eiConsole IDE provide a number of mechanisms that allow you to encrypt and decrypt data. As with all the components of the eiConsole the user is presented with a graphical Interface with easy to configure panels. To configure the Encryption and Decryption Processors on the Processor Configuration tab, the user clicks the Processor Type drop-down and in the example below, selects Asymmetric Decryption.
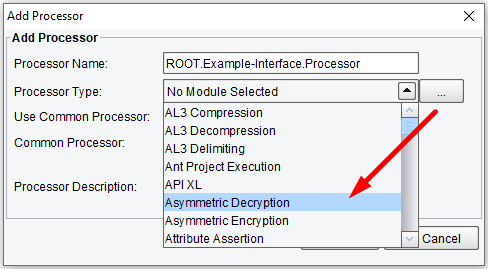
Processor (Adapter) Configuration Drop-Down List
Select the Asymmetric Decryption tab and click on Add Processor.
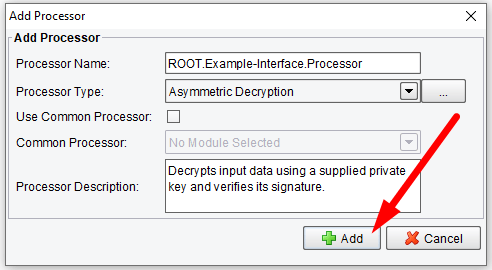
Click on Add Processor
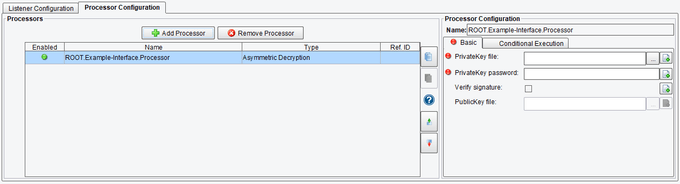
Basic Asymmetric Decryption Processor Configuration Options
The Basic tab allows you to set:
- PrivateKey File – the private key which is utilized to decrypt a data stream encrypted by a public key
- PrivateKey Password – the password to the private key file
- Verify Signature – specifies whether or not to verify that an incoming data stream has been signed with a public-private key pair
- PublicKey File – the public key which was used to sign the data
Asymmetric Decryption Processor Basic Configuration Options
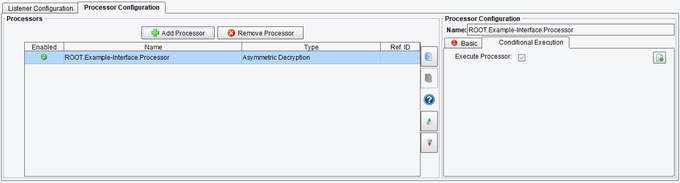
Conditional Execution Asymmetric Decryption Processor Configuration Options
On the Conditional Execution tab, you can set additional Processor execution conditions. The transaction data dependent condition may be specified here as an enhanced expression. If this expression returns anything other than TRUE (ignore case) – this processor will be skipped. No additional configuration for this Processor is required.
Asymmetric Decryption Processor Conditional Execution Configuration Options